Search Results for: software composition analysis
You searched for software composition analysis - DevOps.com

Incorporating Software Composition Analysis into Your Secure Application Strategy
A comprehensive, effective secure application strategy is more important today than ever before. Security breaches are on the rise and the average cost of a data breach is over $3.8 million, according ...

Checkmarx Software Composition Analysis (CxSCA)
As with custom code and commercial software, open source libraries can introduce risks which organizations must identify, prioritize, and address. Security vulnerabilities can leave sensitive data exposed to a breach, license requirements ...
Checkmarx Accelerates Vulnerability Remediation for Open Source Code with New Software Composition Analysis Solution
CxSCA harnesses Checkmarx’s best-in-class automation capabilities to enable developers to find, prioritize, and remediate critical open source vulnerabilities earlier and faster RAMAT GAN, ISRAEL – June 2, 2020 – Checkmarx, the global leader in software security solutions for DevOps, today announced the launch of Checkmarx SCA (CxSCA), ...

Survey: Cyberattacks Aimed at Software Supply Chains are Pervasive
A survey found the vast majority of respondents work for organizations that experienced a software supply chain incident in the past 12 months ...

Secure CI/CD Software Delivery Without Sacrificing Speed and Convenience
It’s a constant battle: The need to deliver new product features quickly while ensuring they are secure and trusted. Organizations are increasingly leveraging automation to make sure DevOps teams and developers are ...

The Role of SBOMs in Software Supply Chain Security
The software supply chain has become increasingly complex and dynamic with the rise of cloud computing, open source software and third-party software components and APIs. Widespread damage can occur if third-party APIs, ...

ReversingLabs: Increased Focus on Software Supply Chain Security
A global survey of 300 global executives, technology and security professionals found software containing vulnerabilities (82%) followed by secrets leaked through source code (55%), malicious code (52%) and suspicious code (46%) posed ...
Software Supply Chain Risk Management: A 2023 Guide
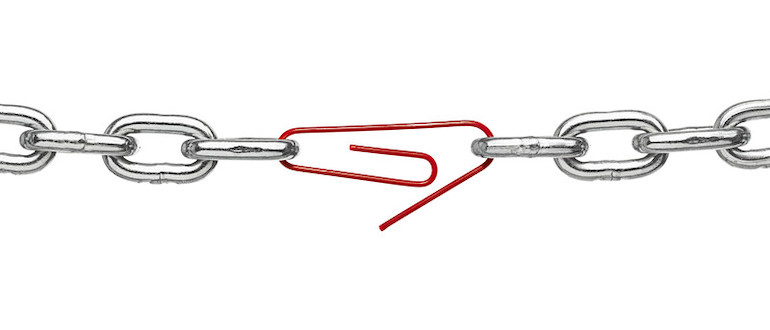
Software supply chain risk management (SSCRM) refers to the process of identifying, assessing and mitigating risks associated with third-party software components and services that are integrated into software products. SSCRM involves understanding ...

Addressing Software Supply Chain Security
It’s essential for organizations to learn more about the software supply chains they rely on and the steps needed to secure them. In just the past few years, we have seen a ...

JFrog Adds Module to Better Secure Software Supply Chains
JFrog today added a JFrog Advanced Security module to its Artifactory repository that enables DevOps teams to scan both binaries and source code for vulnerabilities and misconfigurations. Stephen Chin, vice president of ...

Endor Labs Applies Graph Analysis to Secure Software Supply Chains
Endor Labs exited stealth mode today to launch a platform that applies graph analysis to identify the depth of dependencies that exist within an application. Fresh from raising $25 million in funding, ...

Survey Uncovers Depth of Open Source Software Insecurity
A survey from Snyk and the Linux Foundation published today found that less than half of respondents (49%) work for organizations that have security policies in place for the use or development ...