ZeroNorth today announced it has added a Defect Density Dashboard to its software-as-a-service (SaaS) platform for managing and orchestrating application security scans.
Company CEO John Worrall said Defect Density Dashboard borrows a concept employed to measure software quality and applies it specifically to application security. The dashboard surfaces the number of application security defects per thousand lines of code discovered during scans of code made using software composition analysis (SCA) and software application security testing (SAST) tools.
That metric will create a key performance indicator that application security champions within DevOps teams and chief information security officers (CISO) can use to quantitatively measure the progress being made toward improving overall application security, he said.
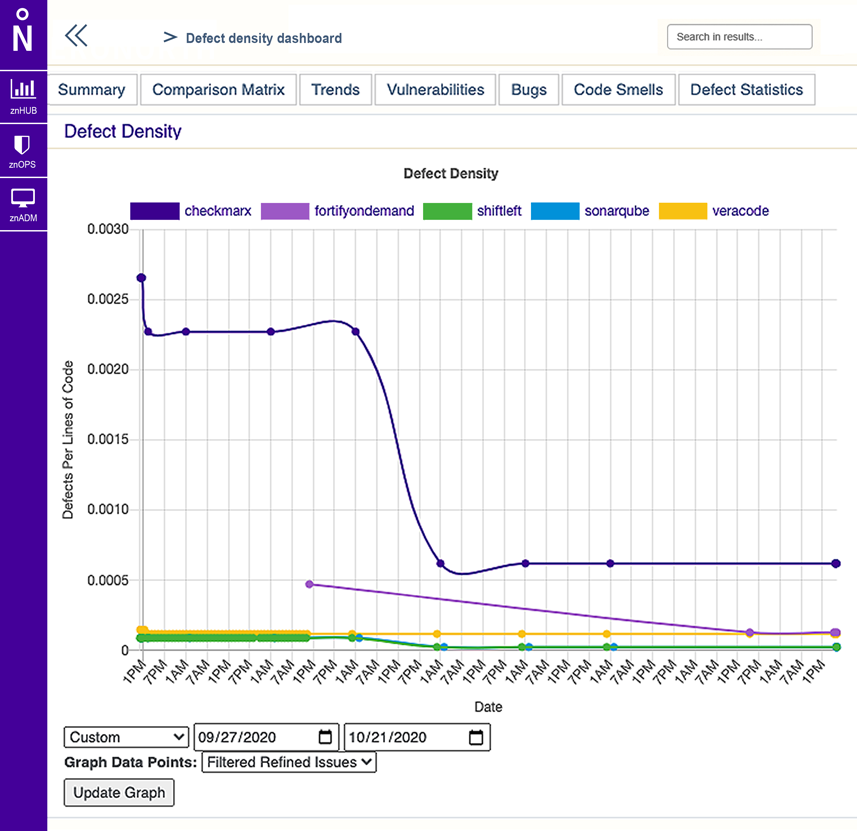
As organizations begin to adopt best DevSecOps practices Worral said one of the challenges IT leaders face is showing the board of directors that the level of investment being made is delivering measurable results. The Defect Density metric applies a concept that is already widely employed by quality assurance teams in manufacturing and other vertical industries to software development, he noted.
As a provider of a SaaS platform for orchestrating security scans across multiple third-party tools, Worral said ZeroNorth is in the unique position of being able to normalize all the data generated by the tools.
The Defect Density Dashboard also makes it easier to identify specific areas of weakness such as larger numbers of SQL injection vulnerabilities that would indicate a need to make additional training available to software development teams, he added, noting that approach allows the application security advocate to be viewed as an ally versus someone who merely criticizes the efforts of a software development team.
Encouraging developers to scan their code before they make a commit is, of course, at the heart of any effort to shift more responsibility for application security to the left. ZeroNorth has been making a case for a platform that makes it easier to implement multiple scans across a DevOps workflow using different tools. That approach makes it more likely that a vulnerability that isn’t discovered by one tool is uncovered by another.
The challenge, of course, is making sure developers scan their code often. There is a natural tendency to delay a scan in the name of productivity. However, the larger the base of code that needs to be scanned, the longer it takes to complete those scans. Most developers would be well-advised to scan smaller amounts of code more often.
Regardless of the approach to scanning, developers should expect to be evaluated based on the number of vulnerabilities that are inadvertently introduced into their code. Cybersecurity teams can no longer keep pace with the rate at which application code is being deployed and updated. As such, many organizations have launched a concerted effort to eliminate as many vulnerabilities as possible before code gets deployed in a production environment. It may never be possible to eliminate 100% of vulnerabilities, but at the very least the most common exploits that cybercriminals actively scan for when looking to compromise an application can be greatly reduced.



