AppDynamics today announced its agent software, which it provides as part of its observability platform, now has the ability to enforce application security policies.
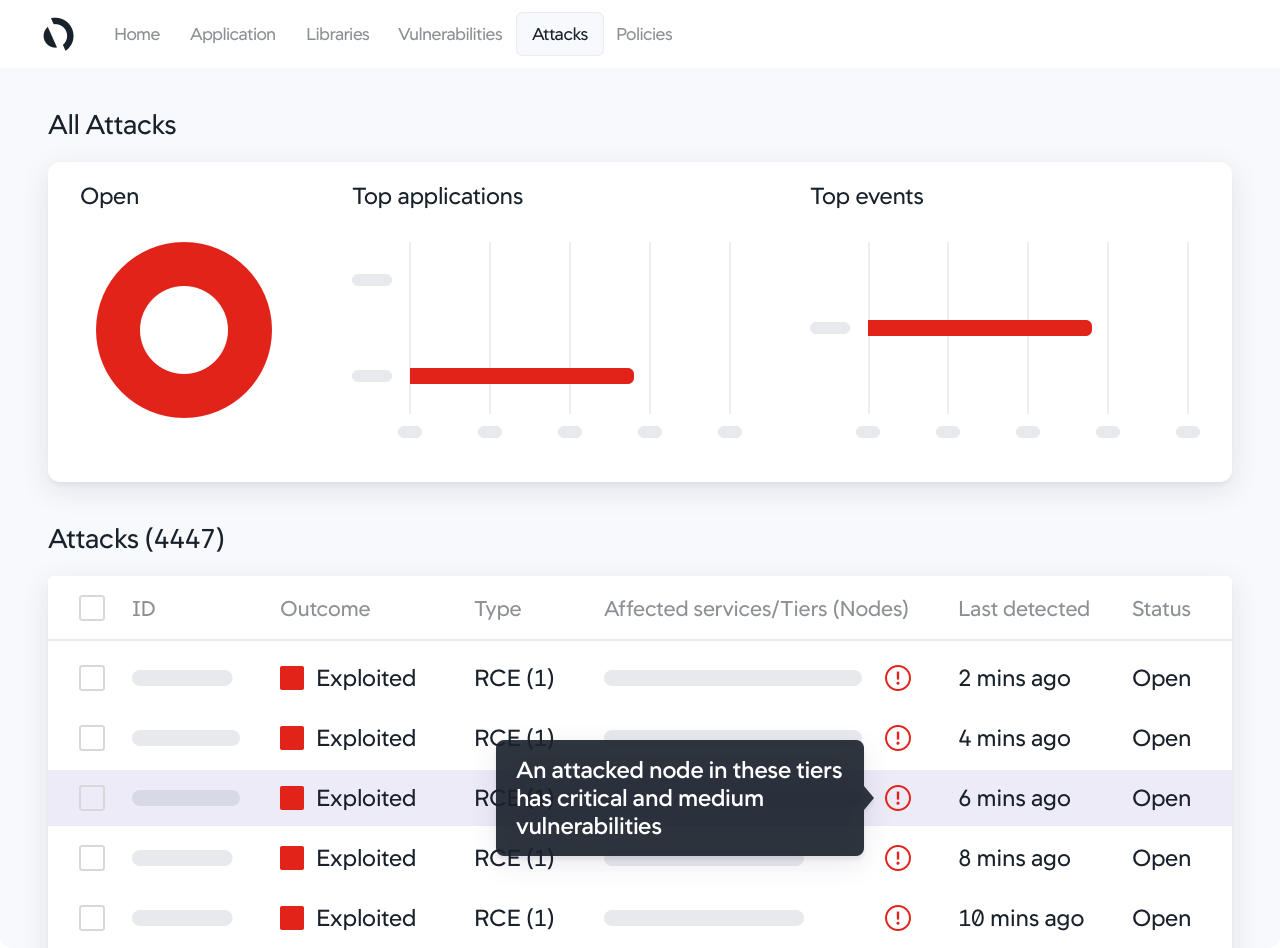
Developed in collaboration with the security business unit of parent company Cisco, the Cisco Secure Application offering, available from AppDynamics, can detect attacks, identify deviations in application behavior and block attacks automatically.
Gregg Ostrowski, a regional CTO for AppDynamics, said the goal is to make it simpler for IT teams that employ AppDynamics for monitoring and observing their IT environments to also embrace DevSecOps best practices. In effect, IT teams can now piggyback security for application runtimes on their existing investment in AppDynamics, Ostrowski said.
The AppDynamics approach provides the added benefit of easy integration with the Cisco security tools to improve collaboration between DevOps and cybersecurity teams, Ostrowski said. Security details correlated with the application topology make it easier to share context in a way that identifies the actual business relevance of any security event, he added.
As organizations accelerate digital business transformation initiatives, Ostrowski said the need to embrace DevSecOps best practices is becoming more urgent. The level of risk attached to these types of projects is significantly higher than with previous generations of applications, Ostrowski said.
While most organizations appreciate the need for greater application security, there’s a debate about how best to achieve that goal. There’s general agreement that developers need to be more involved. However, shifting responsibility for application security to the proverbial left often comes at the expense of developer productivity. AppDynamics is making a case for enabling IT teams, that may already rely on its application performance management (APM) platform, to enforce policies defined by the cybersecurity team.
Of course, there’s still a need to provide developers with the tools required to write more secure code in the first place. The debate is over how involved in the cybersecurity management process developers need to be after applications are deployed in a production environment.
Arguably, the goal should be to enable both teams to accomplish their respective tasks in a way that doesn’t require a constant stream of meetings and updates. In the event a vulnerability is discovered, it’s critical for security teams to determine the threat level that vulnerability represents. Otherwise, remediation of that vulnerability will be just one more item in a long list of patches that developers are already working on.
Regardless of approach, there are now myriad ways to improve overall application security. In effect, the same defense-in-depth approach that IT organizations have relied on to secure network perimeters can now be applied to application security as applications are both constructed and deployed. The most significant challenge is not so much finding the tools required to improve application security, as defining the processes through which best practices can be consistently applied.



