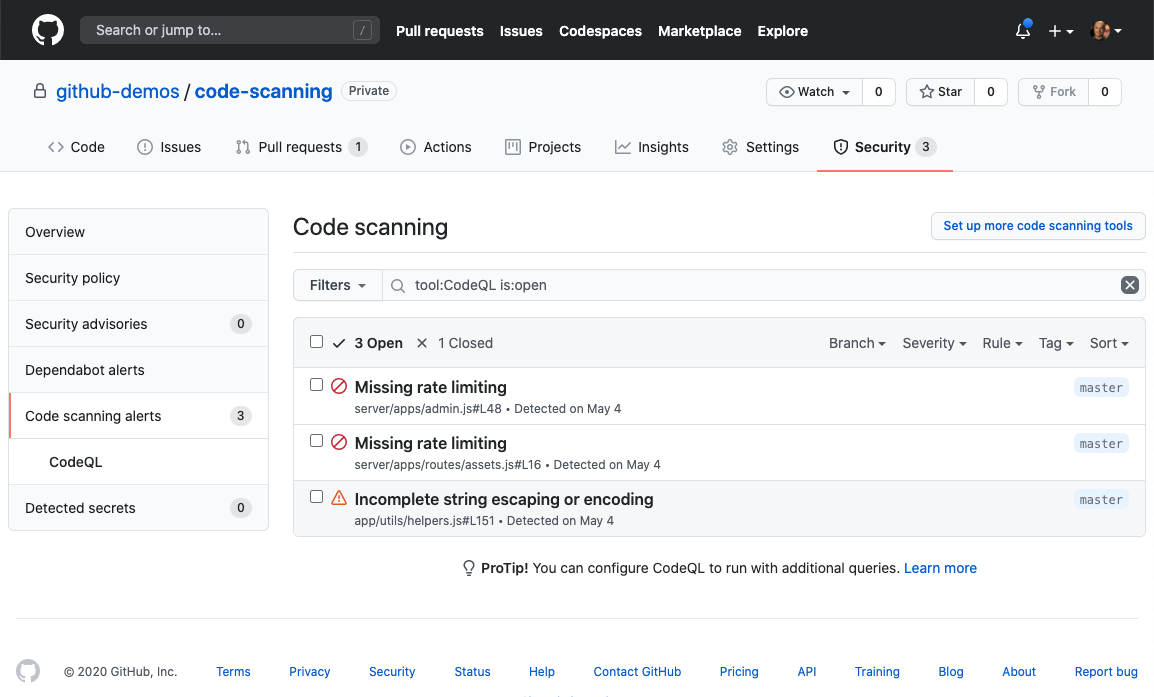
GitHub today announced it is now making available at no cost the open source CodeQL code scanning tool it gained by acquiring Semmle.
Justin Hutchings, a product manager at GitHub, said the goal is to further adoption of best DevSecOps practices by making it easy for developers to scan for vulnerabilities as they check code in and out of the GitHub repository. It is also designed to be integrated with either GitHub Actions or an existing continuous integration/continuous delivery (CI/CD) platform to enable DevOps teams to create workflows that include code scans, he said.
For private repositories, code scanning is part of the GitHub Advanced Security suite of tools GitHub makes available via GitHub Enterprise.
Code scanning also makes it possible to integrate third-party scanning engines via support for the Static Analysis Results Interchange Format (SARIF), which provides a standard for sharing data between SAST tools via a common application programming interface (API). GitHub has thus far partnered with more than a dozen open source and commercial security vendors to allow developers to run code scanning within their offerings, noted Hutchings.
GitHub claims since it made CodeQL available in beta last May, it has scanned more than 12,000 repositories more than 1.4 million times and found more than 20,000 security issues involving everything from remote code execution (RCE) and SQL injection to cross-site scripting (XSS) vulnerabilities.
Developers and maintainers fixed 72% of reported security errors identified in their pull requests before merging in the last 30 days alone, reported GitHub. Hutchings noted those efforts represent a major step forward for DevSecOps, given the fact that industry data shows that less than 30% of all flaws are fixed one month after discovery.
GitHub, along with the open source CodeQL community, has also created more than 2,000 CodeQL queries that DevSecOps teams can employ to scan code for specific types of vulnerabilities. GitHub also noted there already have been 132 community contributions to the CodeQL open source query set.
Given how nascent best DevSecOps practices are in most organizations, simply making SAST tools available to developers is often a major step forward for many organizations. The challenge has been finding SAST tools that developers want to employ, said Hutchings. Most SAST tools were designed for security teams rather than developers. CodeQL is designed to surface vulnerabilities in a way that makes it clear where developers need to prioritize their remediation efforts, he noted.
It’s not clear yet to what degree responsibility for security will shift left toward developers. There will always be a need for cybersecurity teams to verify that the proper controls are in place. However, as DevOps teams assume responsibility for security it’s almost certain they will do so on their own terms. The days when cybersecurity teams select the security tools that developers are expected to employ are now all but over.





